The Untouchables have warned businesses that North Korean hackers are using malicious software to launch a destructive cyberattack in the United States.
The Untouchables have warned businesses that North Korean hackers are using malicious software to launch a destructive cyberattack in the United States.
The alert appeared to describe the one that affected Sony, which would mark first major destructive cyber-attack waged against a company on US soil. Such attacks have been launched in Asia and the Middle East, but none have been seen in the United States. The FBI report did not say how many companies had been victims of destructive attacks.
Analysts think that the attack is a watershed event and that politics now serve as harbingers for destructive cyberattacks.
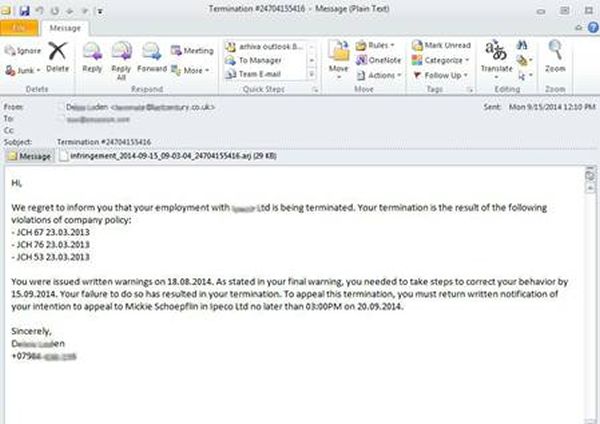
The five-page, confidential “flash” FBI warning issued to businesses last night provided some technical details about the malicious software used in the attack. It provided advice on how to respond to the malware and asked businesses to contact the FBI if they identified similar malware.
The malware overrides all data on hard drives of computers, including the master boot record, which prevents them from booting up.
“The overwriting of the data files will make it extremely difficult and costly, if not impossible, to recover the data using standard forensic methods,” the report said.
The document was sent to security staff at some U.S. companies in an email that asked them not to share the information.
The FBI released the document in the wake of last Monday’s unprecedented attack on Sony Pictures Entertainment, which brought corporate email down for a week and crippled other systems as the company prepares to release several highly anticipated films during the crucial holiday film season.
A Sony spokeswoman said the company had “restored a number of important services” and was “working closely with law enforcement officials to investigate the matter.”
The FBI said it is investigating the attack with help from the Department of Homeland Security. Sony has hired FireEye’s Mandiant incident response team to help clean up after the attack, a move that experts say indicates the severity of the breach.
Hackers used malware similar to that described in the FBI report to launch attacks on businesses in highly destructive attacks in South Korea and the Middle East, including one against oil producer Saudi Aramco that knocked out some 30,000 computers. Those attacks are widely believed to have been launched by hackers working on behalf of the governments of North Korea and Iran.
Sony may have been targeted by North Korea for releasing a film called “The Interview”.
The movie, which is due to be released in the United States and Canada on Dec. 25, is a comedy about two journalists recruited by the CIA to assassinate North Korean leader Kim Jong Un. The Pyongyang government denounced the film as “undisguised sponsoring of terrorism, as well as an act of war” in a letter to U.N. Secretary-General Ban Ki-moon in June.
The FBI report said some of the software used by the hackers had been compiled in Korean, but it did not discuss any possible connection to North Korea.
 McAfee has warned that cryptomining malware has seen a “stunning” growth this year.
McAfee has warned that cryptomining malware has seen a “stunning” growth this year.