 The US FCC was expected to bow to public pressure and allow some semblance of net neutrality in the Land of the Free.
The US FCC was expected to bow to public pressure and allow some semblance of net neutrality in the Land of the Free.
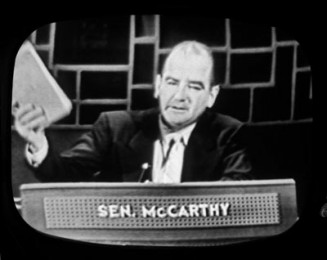
It was to be a brave move – after all a huge chunk of the FCC has connections with phone companies and the watchdog is widely seen as being in the telco pockets.
But the problem was that a huge chunk of the American public had told the FCC that they did not want the telcos strangling their bandwidth or making them pay extra for a reasonable service. In fact, more than four million Americans made it clear to the FCC that they were not going to stand for this thing.
However a new leak shows that the FCC is considering a proposal which it is called a hybrid proposal. It would expand the FCC’s powers to regulate broadband while also allowing cable providers to charge more money for fast lanes.
The “hybrid” proposal now under consideration has not been finalised but according to media leaks and discussions with interested parties they would expand the FCC’s powers to regulate broadband while also allowing a carve out for cable providers to charge more money for fast lanes. However, the rules will only allow the FCC to intervene to promote competition.
The idea is that would not upset the comms companies because they would be allowed to do what they like.
All those people who voted against such a scheme are a little miffed. Apparently, they thought if enough people voted against such a scheme the US government would have to listen. After all the US is supposed to be a democracy and follow the will of the majority and not corporates.
Apparently not.
Protesters having been gathering outside the White House and in a dozen US cities to demonstrate against a “hybrid” solution now being considered to end a stalemate over regulating the internet.