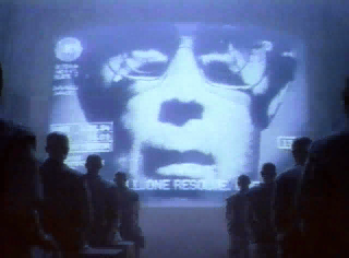
Government plans to make the Information Commissioner’s Office (ICO) responsible for monitoring the use of biometric and DNA data by the police are “ill-conceived”—we think that means “nuts”, according to the UK’s biometrics and surveillance camera commissioner.
Government plans to make the Information Commissioner’s Office (ICO) responsible for monitoring the use of biometric and DNA data by the police are “ill-conceived”—we think that means “nuts”, according to the UK’s biometrics and surveillance camera commissioner.
Fraser Sampson has the job of making sure that that the police collect, retain and use a range of biometric material, including digital facial images, as surveillance camera commissioner his job is to get the cops to comply with the surveillance camera code of practice.
Sampson was appointed to the dual position in March 2021, after the UK Ministry of the Interior announced in July 2020 that it would be amalgamating the roles to make the stand alone statutory functions of each office the responsibility of a single individual.
But the idea of further amalgamating the roles under the purview of the ICO is the brilliant plan of the Department for Digital, Culture, Media & Sport (DCMS) which has currently put the idea out to consultation.
But by “consultation” the government meant not telling anyone about it because it clean forgot to mention it to the bloke who was most affected.