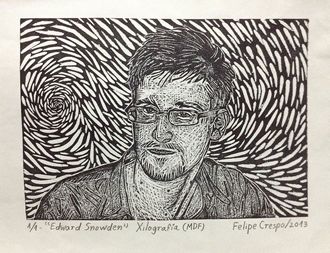
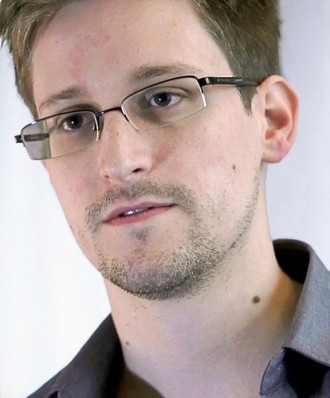
A free email encryption software project which was used by whistleblower Edward Snowden nearly went under this week when the bloke behind it ran out of cash.
A free email encryption software project which was used by whistleblower Edward Snowden nearly went under this week when the bloke behind it ran out of cash.
Koch’s code is behind most of the popular email encryption programs GPGTools, Enigmail, and GPG4Win. If he packed it in, he would create a nightmare scenario for the security industry.
Werner Koch appealed for cash to keep his Gnu Privacy Guard project going. He wrote the software, known as Gnu Privacy Guard, in 1997, and since then has been almost single-handedly keeping it alive with patches and updates from his home in Erkrath, Germany. Now 53, he is running out of money and patience with being underfunded.
He has been running the project more or less for free because he believed there was a need to have some sort of open saucy encrypted software. In 2013 he was all set to pack it in and then the Snowden news broke, and he realised that this was not the time to cancel.
It is not as if the industry has been particularly helpful, despite its dependence on him, the security industry has not been that helpful.
Koch could not raise enough money to pay himself and to fulfill his dream of hiring a full-time programmer. He has been living off $25,000 per year since 2001 — a fraction of what he could earn in private industry. In December, he launched a fundraising campaign that has garnered about $43,000 to date but he needed $137,000 to pay himself a decent salary and hire a full-time developer.
A lifeline was thrown to him this week. He was awarded a one-time grant of $60,000 from Linux Foundation’s Core Infrastructure Initiative. Donations flooded Werner’s website donation page and he reached his funding goal of $137,000. In addition, Facebook and the online payment processor Stripe each pledged to donate $50,000 a year to Koch’s project.
The cash gave Koch, who has an 8-year-old daughter and a wife who isn’t working, some breathing room. But when Propublica http://www.propublica.org/article/the-worlds-email-encryption-software-relies-on-one-guy-who-is-going-broke asked him what he will do when the current batch of money runs out, he shrugged and said he prefers not to think about it. “I’m very glad that there is money for the next three months,” Koch said. “Really I am better at programming than this business stuff.”