If you own hard-drives made by Western Digital, Seagate, and Toshiba all your data could have been seen by US spooks.
If you own hard-drives made by Western Digital, Seagate, and Toshiba all your data could have been seen by US spooks.
According to Kaspersky Lab, the US National Security Agency figured out how to hide spying software deep within hard drives made by Western Digital, Seagate, Toshiba, IBM, Micron and Samsung.
Kaspersky said it found personal computers in 30 countries infected with one or more of the spying programs, with the most infections seen in Iran, followed by Russia, Pakistan, Afghanistan, China, Mali, Syria, Yemen and Algeria. The targets included government and military institutions, telecommunication companies, banks, energy companies, nuclear researchers, media, and Islamic activists, Kaspersky said.
The Russian outfit did not name the US as the country behind the software, but said it was closely linked to Stuxnet, which was a NSA-led effort.
A former NSA employee told Reuters that Kaspersky’s analysis was correct, and that people still in the spy agency valued these espionage programmes as highly as Stuxnet. Another former intelligence operative confirmed that the NSA had developed the prized technique of concealing spyware in hard drives.
Kaspersky published the technical details of its research on Monday, a move that could help infected institutions detect the spying programs, some of which trace back as far as 2001
The announcement could lead to a backlash against Western technology, in countries such as China, which is already drafting regulations that would require most technology suppliers to provide copies of their software code for inspection.
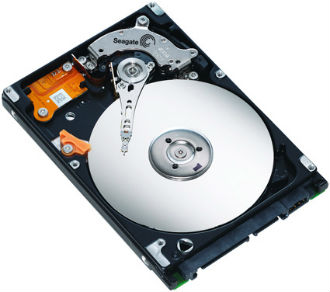
Kaspersky said the spies made a technological breakthrough by figuring out how to lodge malicious software in the obscure code called firmware that launches every time a computer is turned on.
Disk drive firmware is viewed by spies and cybersecurity experts as the second-most valuable real estate on a PC for a hacker, second only to the BIOS code invoked automatically as a computer boots up.
The information was news to Western Digital, Seagate and Micron who said it was the first they had heard of it. Toshiba and Samsung declined to comment and IBM just ignored hacks requests.
 Exertis is launching its Exertis Cybersecurity product throughout Europe.
Exertis is launching its Exertis Cybersecurity product throughout Europe.