One thing that is weird about the Tame Apple Press is that if Apple makes a big cock up it really has nothing to say.
One thing that is weird about the Tame Apple Press is that if Apple makes a big cock up it really has nothing to say.
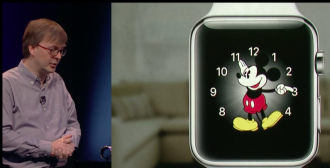
If Apple’s iWatch was even a little bit interesting, the press would have been over the top in its enthusiasm. There would have been a ton of coverage and lots of snaps of the grimly smiling Tim Cook looking like an evil magician on his way to a baby boiling conference.
Sure there was the usual staged Nuremberg rally, where Apple staffers, fanboys and the Tame Apple Press cheered the arrival of the iPhone with the usual standing ovulation. But they would have done that anyway.
What was interesting was how muted the rest of the press coverage was. Warning signs tipped up when the Italian television news, which only reports bollocks like this, gave the iWatch a token 30 seconds. Most of that 30 seconds was a free advert for the iPhone and hardly mentioned the watch at all. By contrast the iPhone 6 got 15 minutes when it launched and Prime Minister of Italy Matteo Renzi smuggly umming and erring his way through a 20 minute speech was covered verbatim.
A search through the wires this morning showed the usual suspects giving an uncharacteristically muted coverage. The News Republic did not even mention the watch, and instead talked about Cook’s tweet about not sleeping before the launch.
So why the disappointed response? Apple’s iWatch has arrived nearly two years behind its rivals and it basically has nothing to offer for its huge price tag $350 price tag.
Apple to enter this limited market had to really wow people with new functionality and it simply didn’t. Jobs’ Mob’s first real “innovation” since the death of Steve was an overpriced copy of what was already on the market.
What could have improved the watch’s chances was a killer app involving health care readings, but beyond a basic heart rate meter Apple could not get it to go.
Another thing which could have made it more interesting was it being independent from its iPhone.
However the watch needs the phone to function, meaning that if you are Christy Turlington Burns and you take the thing on your run you have to lug your heavy iphone with you. If you are carrying the phablet version of the phone that is really heavy. It might make you a better runner to carry all that weight, but since most iPhone users are carrying a few extra pounds anyway it is probably not a good idea.
So if you want the watch for sport, the iWatch does some of what you want, less efficiently, for three times the price of a sports product.
If you want the watch to complement your iPhone then it fails there too. Why do you need something on your wrist that your iPhone already has in your pocket?
All this does not mean the iWatch will fail. In fact it is a screaming indictment of modern civilisation that the iWatch will probably sell in reasonable numbers. Apple might be able to save the product in version two by getting the health functionality going. But they are empty sales. They are people buying something they don’t need, because it has an Apple logo. You can only get away with that so often.
But this is not the sort of product that even the Tame Apple Press wants to peddle. Instead they are wandering away whistling, not daring to point out this Emperor has no clothes on in case Apple blacklists them.
But smarter minds, who are worried that Apple has run out of ideas, are selling their shares. A mate of mine who has had them since the iPhone, dumped the lot when he heard that Apple had removed a ton of health functionality from the product. He reasons that ultimately Apple will fail because it has become too big and run out of ideas. The iWatch proves it.